- Details
- Written by Jon Moore
I recently discovered a bug in a product called Rumble (Rumble.run), a network discovery tool. A ticket was opened with support, and while they understood the nature of the situation, they kept blaming the target as being "at fault", despite all evidence provided to the contrary. In my opinion, this problem is more than a simple odd annoyance; it represents a way to evade detection entirely. In this article, we'll go over how to accomplish this, and it's potential ramifications.
- Details
- Written by Jon Moore
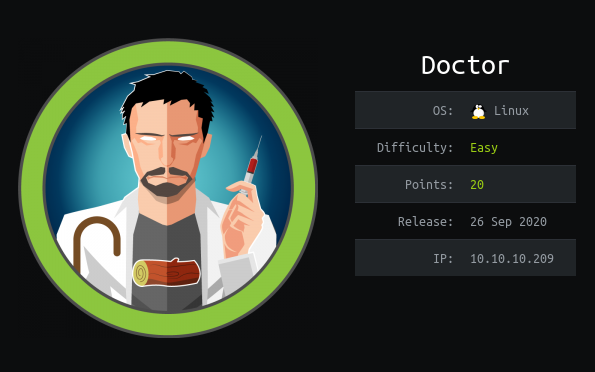
Doctor was a fun box. Though I took a few days here and there to get it done, the bulk of my work was done in 3 or so hours, so it wasn't TOO difficult...
- Details
- Written by Jon Moore
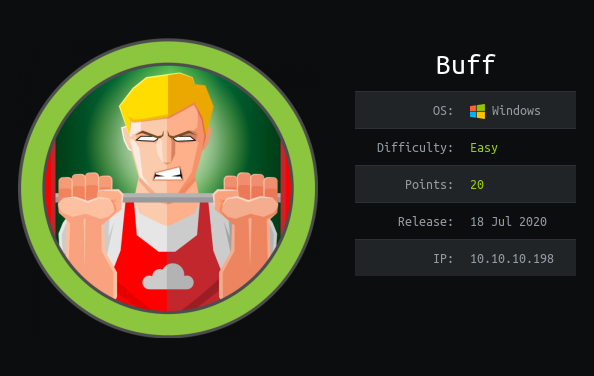
Buff was a... frustrating box. Not only were there mulitple attack vectors, but I discovered a new "rule" put in place by HTB to protect it's users. Though it took me a bit longer than I had hoped, persistence pays off, and I eventually got the root flag.
- Details
- Written by Jon Moore
Laboratory was an Easy Linux box. It certainly drove me down many a rabbit-hole, chasing many red herrings, but ultimately, persistence paid off, and I got the box.
- Details
- Written by Jon Moore
Today I tackle Forest, an Easy Windows box. This one's all about LDAP, my achilles heel. In the end, it actually took me 2 days... :S
Page 2 of 11